NatSecTech - C5ISR Warfare Needs Organizational Transformation
By Navneet Bhushan
More than 100 years back, in 1917, the Soviet people had overthrown an unpopular czar and made modernization a priority. The new Soviet Government – The Communist Government - chose to opt for one of the emerging communications technologies – the loudspeakers. Instead, they could have chosen the other emerging communication technology, i.e. the telephone.
In an interesting book called, Creation of the Media, Paul Starr, explains, “Down to its collapse in 1991 the Soviet Union and the countries under its control had markedly fewer telephones than the countries of Western Europe and North America”.
The bigger problem one should see, as stated by Brafman and Beckstrom in their 2006 book titled, The Starfish and the Spider – the unstoppable power of leaderless organizations, is that “Soviets focused on technology that reflected imperial values: higher-ups telling the common people what to do” via loudspeakers like modern governments do via controlled and sponsored television primarily.
It so transpired that peer-to-peer communication provided by telephone technology proved to be much more powerful than the one-way command of loudspeakers dishing out government propaganda. First of all the telephone created a communication network, and later enabled a broadcast and a distributed internet. At the root of these trends in history is a realization and utilization of great power that humanity learnt – that of distributed, decentralized, peer-to-peer and peer-to-many multi-dimensional connectivity.
The Century of Decentralization
In the evolution of decentralization in the last 100 years or so, despite the forces of centralized command and control in the form chosen as few commanding the commoners, the myth of the need for a strong leader has been busted.
We have witnessed the power of connections and power of many who connect to form networks of influence, craft and change. The evolution of technology from the telephone via internet connectivity and potentially future Brain-Machine Interface, have all brought to play the hidden power and capability of the distributed, de-centralized and above all self-organizing capabilities of complex systems.
Complexity increases not only with the size/numbers of the nodes/elements but much more rapidly with the richness of their interconnections. The human brain has one hundred billion neurons. Each neuron has about 7000 synapses (connections to other neurons) that are about 1 quadrillion connection that gets developed over the years a human brain evolves.
Although size or quantity does matter, the level of the interaction complexity between elements of a system and the environment is key to understanding the power of content-rich networks. From the understanding of these powerful and content-rich networks, new fields have emerged – systems thinking, complexity theory, chaos theory, and catastrophe theory. Sciences of networks and deeper analysis of social networks are challenging us to find new rules or models to comprehend the world that we are in and predict how the world will evolve in future.
Rules of Leaderless-ness
Nassim Nicholas Taleb in his book, Anti-Fragile, claims, “In a democracy, the incentive is to always promise a better outcome than the other guy, regardless of the actual, delayed cost”. One can safely add to this, “without regard to the actual harm”.
Our governments have established democratic form as defined in the old world but not taking into account the pace at which the world is changing or has already changed through connectivity. The world today is becoming extremely decentralized and hence we need to look at new rules of decentralization.
Brafman and Beckstrom describe various rules of decentralizing world. These rules characterize the decentralized organizations as small nodes connected into large networks utilizing the network effects, in messy and chaotic ways. These nodes utilize distributed knowledge by trusting and accepting every other actor of the network. These structures lead to robust organizations that regenerate the whole network even after the severe destruction of the network.
Surprisingly, these distributed organizations are leaderless but have many catalysts – the change agents who show the path and guide but then let go of the nodes/elements/actors on their own ways of doing things in the network. This is because at the core of these organizations is some shared value or ideas.
Many of these rules are opposite to centralized command and control structures. For example, one rule says that in decentralization organization it is better to be vaguely right than to be precisely wrong. The final rule says if you cannot defeat them join them. Fighting the forces of decentralization is best futile and at worst counterproductive.
The metaphor used for decentralized organizations and populations is the starfish. The decentralized organizations are revolutionary, relying on the power of peer to peer relationships. In contrast, the traditional government is what can be termed as the Spider organization. The spider with a visible head is easy to kill, counter or eliminate. Just go for the head. Starfishes and salamanders are known to be able to regenerate their limbs completely. The Starfish is a decentralized living being and hence more anti-fragile- using Taleb’s term for things that gain from harm.
Information Age Contradictions
Sun Tzu, the ancient war theorist from China states, “War is a matter of vital importance to the state”. The question that should be asked today and in future is how much of importance does war gives to the state? War existed before nation-states came into existence somewhere in the 17th Century. Crime, Causes and Communities that cut across national boundaries have started emerging as higher-level identities that unify more people than the national identities.
The world in the last three decades or so is seeing a remarkable conflict. It is a conflict between the Command and Control Organizations on one side and the newer Decentralizing Organizational on the other side.
As the individual is becoming more connected, the State and its institutions, however, continues to be a Spider - the bureaucratic, centralized, slow, hierarchical, command and control pyramids that have stood the test of time in a disconnected or low connected world of the past.
The west, led by the US, enjoyed the demise of communism when Perestroika and Glasnost failed to stem the power of decentralization in the erstwhile Soviet Union in the late 1980s. However, as it is becoming painfully clear when individuals connect and create decentralized organizations in the form of starfishes, the spiders need to assimilate themselves in the change vortex by following the way of starfishes.
Towards C5ISR Warfare
We do not need Che Guevara or a Mao in the connected world – who defined and developed the guerilla warfare in modern times. The adversaries today are more aware, are more connected and have the ability to self-organize. The governance model has to be looked at deeply in the light of distributed information.
Decentralized self-organizing connected individuals cannot be governed by a centralized decision-making system. If the governance models do not change, the non-state actors as an instrument of warfare will become more and more powerful. It is possible that war may evolve to exist independent of the state. State-less war could be a possible future.
The Four Generations of Warfare
The soldiers of the state military organizations are up against their centralized, controllers who have been dishing out first and second-generation warfare structures with an absolute focus on control through from of commands in an orderly, structured, and almost mechanistic way alien to the true nature of a human being in a highly connected world.
The third generation warfare, also called the manoeuvre warfare, was a German construct which they utilized in World War I through infantry, giving options for soldiers and units to take initiative in the situation as is and take proactive actions as per context, situation and the adversary; rather than waiting for orders from a remote commander.
This German construct of Command with reduced control in the form of third-generation warfare that was greatly successful in World War II against France and other nations who continued to be organized for combat in first-generation and second-generation warfare. Germans used the Panzer divisions for what they called Blitzkrieg.
The fourth generation warfare as defined by Lind is between Cultures, Causes and even Criminals and Nation-States. The reader can refer to Lind’s article [[i] ] to understand the typology of generational warfare. This typology has been criticized by others though and LIC/terrorist warfare and High tech warfare differentiation of 4th Generation Warfare can also be referred [[ii]].
The key point, however, is the state has an option today to transform itself to the ways of the decentralized world through technological interconnecting means. This is especially true for the military forces of hierarchical command and control organizational structures. One clear indication in the military force structure evolution is visible in the way the combat support system orchestrate control over combat forces through the command of the authority evolved. The Command and Control (C2) evolved first to Command, Control, Communications, Intelligence (C3I) then computer was added to become C4ISR.
It is with the integration of combat with systems into the C4ISR system gives C5ISR – a wholistic template for forces of future. The C5ISR warfare will have human-machine teaming achieved through the next wave of technologies that are going to change the way war is conducted. The challenge is to transform the hierarchical organization of military of previous generations of warfare to collaborative, learning and emergent organizations.
C5ISR Warfare needs
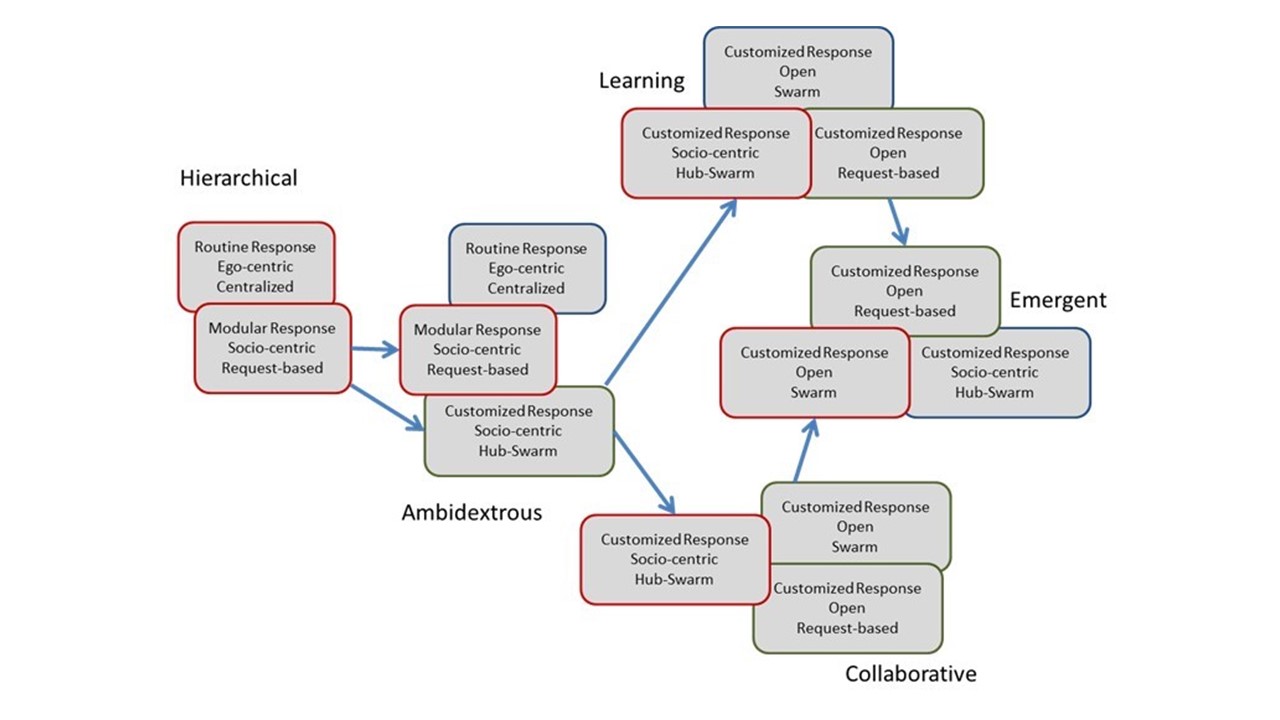
In our paper, Organizational Forms and Social Network Types – A Framework for Analysis [[iii]], we identified five types of organizational forms as hierarchical, ambidextrous, collaborative, learning and emergent organizational structures that were defined and described in the literature. We further identified the classification of different social networks available in different contexts.
Using this study, we defined five types of social networks that are useful and meaningful on three key dimensions (1) The type of response that these networks generate i.e., what kind of output the networks can generate (three different types of responses are customised response, modular response and routine response, (2) the second dimension is the centrality of the networks - in this dimension also there are three types - ego-centric (individuals at the centre with their network), socio-centric networks where boundaries of the network are clear and finally, open networks where boundaries are not necessarily clear, (3) the third dimension is the network architecture - where we have four options centralized networks, request based networks, hub swarms and swarms. Combining these three dimensions one can in principle get 3x3x4 = 36 different Network types. However, we have selected five different types of Social Networks as described below.
Customized Response Open Swarms (CROSs) – These types of social networks usually do not have any clear boundaries. They have nearly identical nodes in terms of their capabilities and authority. These nodes come together to respond to problems through a process of creating shared awareness, quickly formulating the problems and solving problems by leveraging each other's capabilities collectively. After problems are responded to, they go to the next problems or keep on building their capabilities. These networks typically create customized responses to unstructured problems.
Modular Response Socio-Centric Request-Based (MRSR) – These types of social networks have clear boundaries and typically generate solutions through a combination or re-sequencing of components of the over-all solutions. They work in an environment when components of the problems and solutions are known but constructing the solution requires a combination of components in a non-trivial way. Further, the nodes of these networks have the same value but different capabilities and they respond to the problems by requesting each other to provide their unique capabilities to solve problems through modularized responses.
Routine Response Ego-Centric Centralized (RECC): These types of social networks create routine responses to structured problems. There is typically a centralized hub of high value which has low-value nodes connected. The centralized hubs of different sub-nets have their own ego-centric networks based on the network of the leader of the hub. However, the low-value nodes of a subnet do not connect to low-value nodes of other subnets.
Customized Response Socio-Centric Hub-Swarm (CRSH): These types of social networks have one or more high-value hubs besides a large number of nearly equal value nodes. These nearly equal value nodes swarm together for solving an unstructured problem with the high-value hubs. Each subnet may have its own high-value hub and many equal value nodes that can create a shared picture of the problems which gets picked and responded to through swarming in a slightly controlled manner.
Customized Response Open Request-Based (CROR): These types of social networks do not have clear boundaries. However, the customized response is created through a request-based mechanism.
Our paper and analysis provide a transformation road map for any hierarchical organization to transform itself into collaborative, Learning and Emergent organization forms through the transformation of the way they orchestrate their social networks.
Key Message
The Network Centric Warfare is now C5ISR warfare. The technology, of course, is the key attribute of this new form of warfare – perhaps a new generation if we follow the war generations typology. The key, however, is that human component of the way militaries are organized need to transform themselves from rigid hierarchies of command and control based orderly structures to collaborative, learning and emergent organization forms which they transform as and when it is needed. The technology can make these network structures malleable, but can our mindsets be transformed –how soon?
NatSecTech (National Security Technology) is a fortnightly column covering Futures, Analysis, Architecture, Innovation, Design and Assessment (FAAIDA) of technologies involved in national security.
 *Author worked as a Defence Scientist from 1990-2000. He is founder director of CRAFITTI CONSULTING (www.crafitti.com) – a Strategy, Technology, Innovation and Intellectual Property Consulting firm focused on co-crafting solutions for global problems. He regularly writes on defence and security. He is the principal author of Strategic Decision Making- Applying the Analytic Hierarchy Process published by Springer-Verlag, UK, as part of the Decision Engineering Series. Navneet Blogs at http://innovationcrafting.blogspot.com.He can be contacted at navneet(dot)bhushan(at) crafitti(dot)com
*Author worked as a Defence Scientist from 1990-2000. He is founder director of CRAFITTI CONSULTING (www.crafitti.com) – a Strategy, Technology, Innovation and Intellectual Property Consulting firm focused on co-crafting solutions for global problems. He regularly writes on defence and security. He is the principal author of Strategic Decision Making- Applying the Analytic Hierarchy Process published by Springer-Verlag, UK, as part of the Decision Engineering Series. Navneet Blogs at http://innovationcrafting.blogspot.com.He can be contacted at navneet(dot)bhushan(at) crafitti(dot)com
Ref.
i https://original.antiwar.com/lind/2004/01/15/understanding-fourth-generation-war/
ii https://indianstrategicknowledgeonline.com/web/4Th%20GENRATION%20WARFARE%20ANOTHER%20LOOK.pdf
